Read the Full Series
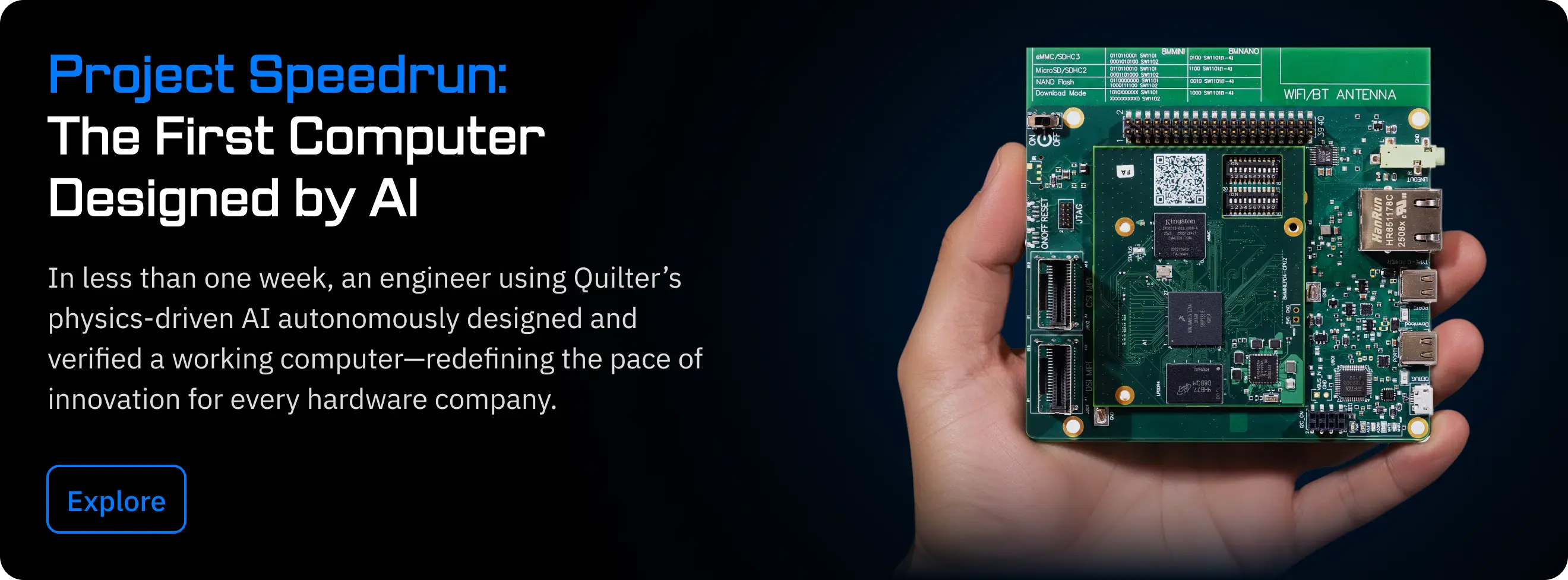
This article is one part of a walkthrough detailing how we recreated an NXP i.MX 8M Mini–based computer using Quilter’s physics-driven layout automation.
If you’ve evaluated Quilter, or any cloud-based engineering tool, you’ve probably had the security conversation. Maybe you’ve had it multiple times: once with your team, once with IT, and once with procurement. We hear the same questions in nearly every conversation with engineering leaders:
Where does my data go? Who can see it? Are you training on my designs?
These are the right questions to ask. And as of this month, we have an independently verified answer: Quilter is SOC 2 Type II compliant.
What SOC 2 Type II Actually Covers
SOC 2 is a compliance framework developed by the AICPA that evaluates how a SaaS provider protects customer data. There are two types. Type I checks whether security controls are designed correctly at a single point in time. Type II is more rigorous: the auditor evaluates whether your security controls are working effectively over an extended observation period, typically 3 to 12 months.
In practical terms, SOC 2 Type II means an independent auditor reviewed Quilter’s cloud infrastructure, access controls, data handling procedures, incident response processes, and availability practices — and confirmed that they work, consistently, over time.
What This Means for You
If you’re an engineer evaluating Quilter, the short version is: your design data is protected by enterprise-grade controls, and we can prove it. Here are the specifics:
- Isolated workspaces. Each customer operates in their own secure workspace on AWS. No one outside your organization, including other Quilter customers, can access your data.
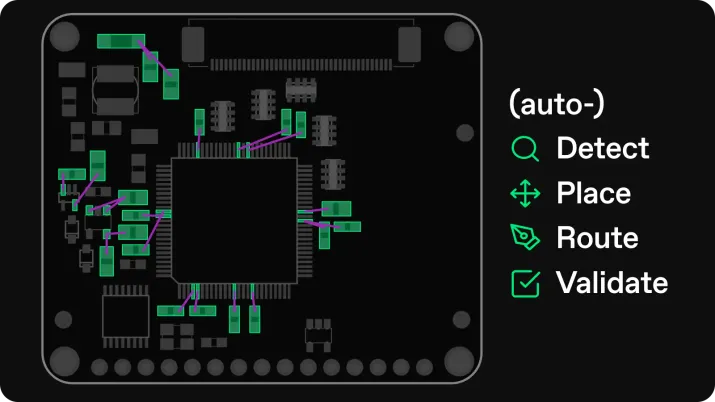
- No data training. Quilter is not a large language model. We train our AI through reinforcement learning on synthetic data. We don’t ingest, read, or learn from any customer designs. Your IP stays yours.
- You own your output. When Quilter places and routes your board, the result belongs to you. We’re a tool, not a co-author.
- Data access on your terms. We don’t look at your designs unless you explicitly ask us to — for example, during a guided pilot where our engineering team helps you get the best results.
If you’re in IT or procurement, you can request the full SOC 2 Type II report. We’re happy to support your vendor security review and answer any follow-up questions.
Why This Matters Now
We’ve talked with engineering teams at companies where security review timelines add weeks or months to a pilot decision. SOC 2 Type II changes that. It’s a standard artifact that IT and procurement teams recognize and can evaluate against their own requirements.
This doesn’t mean security review disappears entirely — many organizations have additional requirements, and we expect that. But it gives your internal teams a verified starting point instead of a blank questionnaire.
On-Premise Option
For organizations that need to go further, ITAR-controlled programs, classified environments, or any situation where cloud isn’t an option, Quilter is also available as an on-premise deployment. You run it on your own infrastructure. The software is identical; only the hosting model changes.